Some instructions on how to get started with using the ansible to automate Cisco ACI specifically by using ansible playbooks to accomplish basic tasks.
Using the Cisco ACI GUI can be time-consuming and error prone, a more efficient could be to automate the process using ansible playbooks. Ansible is essentially an automation tool that uses playbooks consisting of Yaml files to automate the process of network configuration via connection to the APIC REST interface and push the config API commands.
Really useful link for how to get your Windows environment set up for using ansible, including Cygwin and Linux virtual machines:
https://phoenixnap.com/kb/install-ansible-on-windows#htoc-method-1-using-cygwin
I have found the Cygwin approach to work perfectly fine for running ansible. In fact, I recommend Cygwin as the way to go in running ansible in your Windows environment, given that all my attempts to install via ‘pip install’ commands failed. The number of Stack Overflow posts reporting similar problems will testify to this.
To cd to a C:\ drive using Cygwin use this:
For this post I installed ansible via enabling Ubuntu on Windows as yet another alternative approach. This is adequately described on the previous link, but summarised as follows. To install, first type in- and search for ‘Turn Windows features on or off’ in your Start menu, select the ‘Windows Subsystem for Linux’ checkbox option, click OK and restart your machine for the change to take effect. Then open Microsoft Store via the Start menu , type in ‘Ubuntu’ and install. Once installed, use the following command line instructions to install ansible:
[code language="xml"]
$ sudo apt-get update
$ sudo apt-get install software-properties-common
$ sudo apt-add-repository ppa:ansible/ansible
$ sudo apt-get update
$ sudo apt-get install ansible -y
Some example inventory and Yaml files here:
inventory.txt
[apic] sandboxapicdc.cisco.com username=admin password=!v3G@!4@Y
tenants.yml
Some Yaml playbook code to list all of the tenant information contained in the example Cisco ACI sandbox:
- name: Query all tenants
hosts: apic
connection: local
gather_facts: no
tasks:
- name: TASK 1 - GATHER TENANTS
aci_tenant:
hostname: "{{ inventory_hostname }}"
username: "{{ username }}"
password: "{{ password }}"
validate_certs: no
state: query
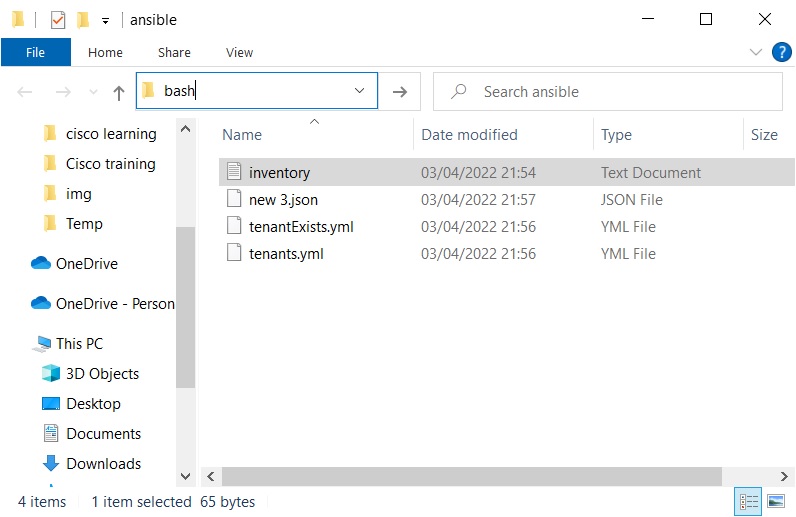
To run this ansible playbook, launch the Ubuntu terminal and navigate to the Windows directory to where your inventory and .yml files are stored. An easy way to navigate to the folder is to open the contents of the Windows folder in File Explorer and type ‘bash’ in the address bar:
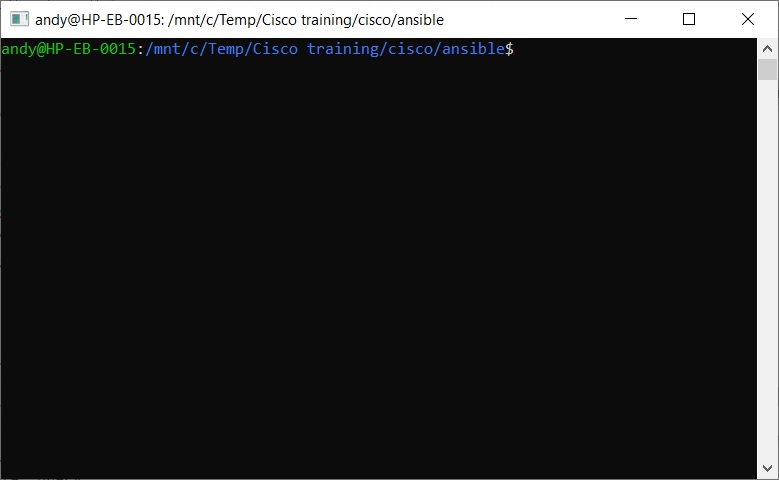
Then hit Enter. This will provide the address you need to cd to:
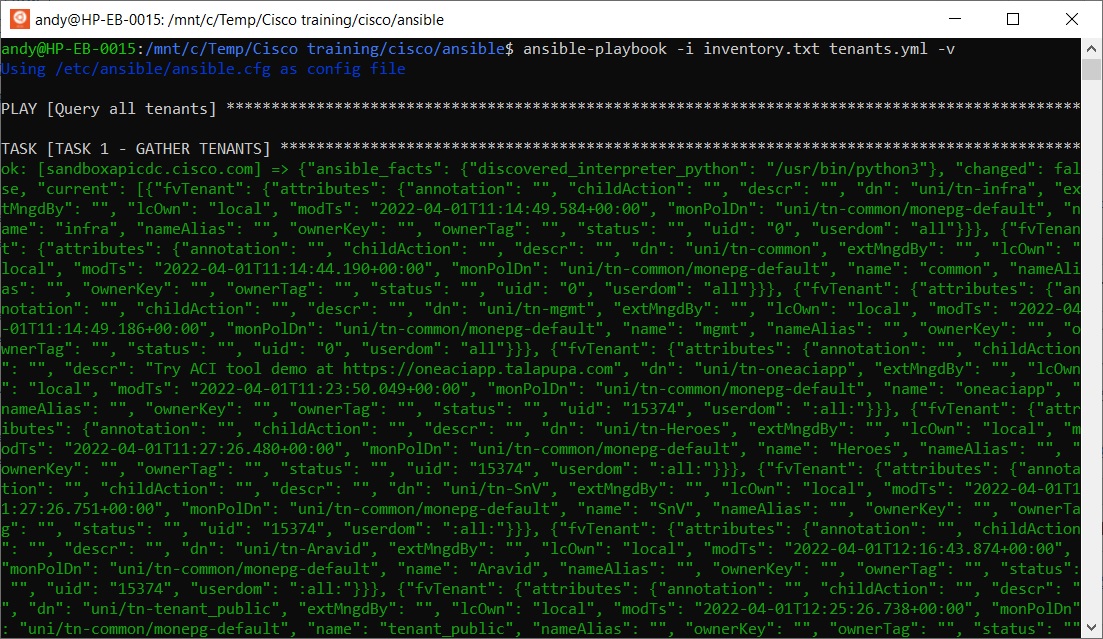
Now run the following ansible command:
ansible-playbook -i inventory.txt tenants.yml -v
This returns the Tenants as a set of JSON objects as shown:
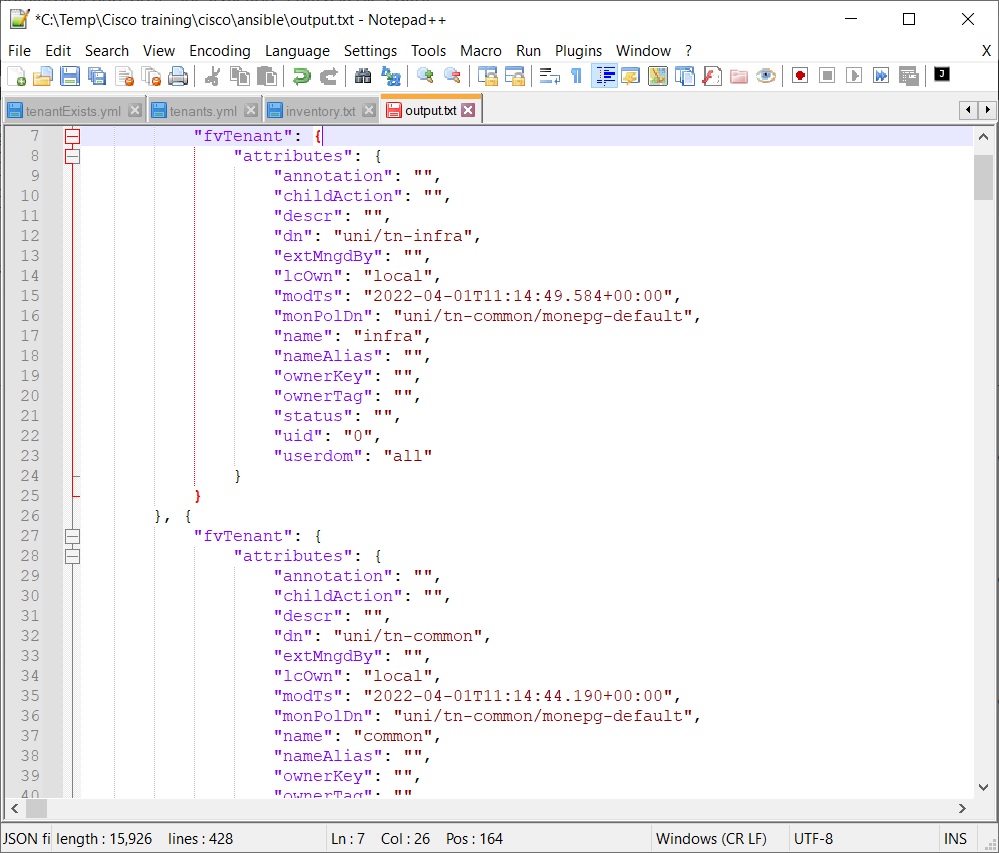
As viewed in json-prettified format in Notepad++:
More ansible examples.
specificTenant.yml
A task to return just the data about the tenant called infra.
- name: Query a specific tenant
hosts: apic
connection: local
gather_facts: no
tasks:
- name: TASK 1 - SPECIFIC TENANTS
aci_tenant:
hostname: "{{ inventory_hostname }}"
username: "{{ username }}"
password: "{{ password }}"
validate_certs: no
state: query
tenant: infra
JSON Output:
ok: [sandboxapicdc.cisco.com] => {
"ansible_facts": {
"discovered_interpreter_python": "/usr/bin/python3"
},
"changed": false,
"current": [{
"fvTenant": {
"attributes": {
"annotation": "",
"childAction": "",
"descr": "",
"dn": "uni/tn-infra",
"extMngdBy": "",
"lcOwn": "local",
"modTs": "2022-04-04T10:29:55.139+00:00",
"monPolDn": "uni/tn-common/monepg-default",
"name": "infra",
"nameAlias": "",
"ownerKey": "",
"ownerTag": "",
"status": "",
"uid": "0",
"userdom": "all"
}
}
}
]
}
epgs.yml
A task to return all EPG information from an existing ACI fabric.
- name: Query all EPGs
hosts: apic
connection: local
gather_facts: no
tasks:
- name: TASK 1 - GATHER EPGs
aci_epg:
hostname: "{{ inventory_hostname }}"
username: "{{ username }}"
password: "{{ password }}"
validate_certs: no
state: query
JSON Output:
ok: [sandboxapicdc.cisco.com] => {
"ansible_facts": {
"discovered_interpreter_python": "/usr/bin/python3"
},
"changed": false,
"current": [{
"fvAEPg": {
"attributes": {
"annotation": "",
"childAction": "",
"configIssues": "",
"configSt": "applied",
"descr": "",
"dn": "uni/tn-infra/ap-ave-ctrl/epg-ave-ctrl",
"exceptionTag": "",
"extMngdBy": "",
"floodOnEncap": "disabled",
"fwdCtrl": "",
"hasMcastSource": "no",
"isAttrBasedEPg": "no",
"isSharedSrvMsiteEPg": "no",
"lcOwn": "local",
"matchT": "AtleastOne",
"modTs": "2022-04-04T10:30:32.198+00:00",
"monPolDn": "uni/tn-common/monepg-default",
"name": "ave-ctrl",
"nameAlias": "",
"pcEnfPref": "unenforced",
"pcTag": "32771",
"pcTagAllocSrc": "idmanager",
"prefGrMemb": "exclude",
"prio": "unspecified",
"scope": "2523136",
"shutdown": "no",
"status": "",
"triggerSt": "triggerable",
"txId": "5764607523034234882",
"uid": "0",
"userdom": "all"
},
"children": [{
"fvRsBd": {
"attributes": {
"annotation": "",
"childAction": "",
"extMngdBy": "",
"forceResolve": "yes",
"lcOwn": "local",
"modTs": "2022-04-04T10:29:55.139+00:00",
"monPolDn": "uni/tn-common/monepg-default",
"rType": "mo",
"rn": "rsbd",
"state": "formed",
"stateQual": "none",
"status": "",
"tCl": "fvBD",
"tContextDn": "",
"tDn": "uni/tn-infra/BD-ave-ctrl",
"tRn": "BD-ave-ctrl",
"tType": "name",
"tnFvBDName": "ave-ctrl",
"uid": "0",
"userdom": "all"
},
"children": [{
"fvSubnetBDDefCont": {
"attributes": {
"bddefDn": "uni/bd-[uni/tn-infra/BD-ave-ctrl]-isSvc-no",
"childAction": "deleteNonPresent",
"lcOwn": "local",
"modTs": "2022-04-04T10:29:49.718+00:00",
"monPolDn": "",
"name": "",
"nameAlias": "",
"rn": "subnetBddefDn-[uni/bd-[uni/tn-infra/BD-ave-ctrl]-isSvc-no]",
"status": ""
}
}
}
]
}
}, {
"fvRsCustQosPol": {
"attributes": {
"annotation": "",
"childAction": "",
"extMngdBy": "",
"forceResolve": "yes",
"lcOwn": "local",
"modTs": "2022-04-04T10:29:55.139+00:00",
"monPolDn": "uni/tn-common/monepg-default",
"rType": "mo",
"rn": "rscustQosPol",
"state": "formed",
"stateQual": "default-target",
"status": "",
"tCl": "qosCustomPol",
"tContextDn": "",
"tDn": "uni/tn-common/qoscustom-default",
"tRn": "qoscustom-default",
"tType": "name",
"tnQosCustomPolName": "",
"uid": "0",
"userdom": "all"
}
}
}
]
}
}, {
"fvAEPg": {
"attributes": {
"annotation": "",
"childAction": "",
"configIssues": "",
"configSt": "applied",
"descr": "",
"dn": "uni/tn-infra/ap-access/epg-default",
"exceptionTag": "",
"extMngdBy": "",
"floodOnEncap": "disabled",
"fwdCtrl": "",
"hasMcastSource": "no",
"isAttrBasedEPg": "no",
"isSharedSrvMsiteEPg": "no",
"lcOwn": "local",
"matchT": "AtleastOne",
"modTs": "2022-04-04T10:30:31.824+00:00",
"monPolDn": "uni/tn-common/monepg-default",
"name": "default",
"nameAlias": "",
"pcEnfPref": "unenforced",
"pcTag": "16387",
"pcTagAllocSrc": "idmanager",
"prefGrMemb": "exclude",
"prio": "unspecified",
"scope": "16777199",
"shutdown": "no",
"status": "",
"triggerSt": "triggerable",
"txId": "5764607523034234882",
"uid": "0",
"userdom": "all"
},
"children": [{
"fvRsBd": {
"attributes": {
"annotation": "",
"childAction": "",
"extMngdBy": "",
"forceResolve": "yes",
"lcOwn": "local",
"modTs": "2022-04-04T10:29:55.139+00:00",
"monPolDn": "uni/tn-common/monepg-default",
"rType": "mo",
"rn": "rsbd",
"state": "formed",
"stateQual": "none",
"status": "",
"tCl": "fvBD",
"tContextDn": "",
"tDn": "uni/tn-infra/BD-default",
"tRn": "BD-default",
"tType": "name",
"tnFvBDName": "default",
"uid": "0",
"userdom": "all"
},
"children": [{
"fvSubnetBDDefCont": {
"attributes": {
"bddefDn": "uni/bd-[uni/tn-infra/BD-default]-isSvc-no",
"childAction": "deleteNonPresent",
"lcOwn": "local",
"modTs": "2022-04-04T10:29:49.718+00:00",
"monPolDn": "",
"name": "",
"nameAlias": "",
"rn": "subnetBddefDn-[uni/bd-[uni/tn-infra/BD-default]-isSvc-no]",
"status": ""
}
}
}
]
}
}, {
"fvRsCustQosPol": {
"attributes": {
"annotation": "",
"childAction": "",
"extMngdBy": "",
"forceResolve": "yes",
"lcOwn": "local",
"modTs": "2022-04-04T10:29:55.139+00:00",
"monPolDn": "uni/tn-common/monepg-default",
"rType": "mo",
"rn": "rscustQosPol",
"state": "formed",
"stateQual": "default-target",
"status": "",
"tCl": "qosCustomPol",
"tContextDn": "",
"tDn": "uni/tn-common/qoscustom-default",
"tRn": "qoscustom-default",
"tType": "name",
"tnQosCustomPolName": "",
"uid": "0",
"userdom": "all"
}
}
}
]
}
}
]
}